05 Feb 21
0 VIEWS
0 FAVS
In the business world, it is very common for people to communicate in different languages when doing business overseas. Especially if your company is an international business, communicating effectively in different languages so as to get things done overseas is something that is inevitable.
The number may seem staggering, but Spanish is the native language for more than 340 million people and the number grows every day.
05 Feb 21
Many customers are right now choosing internet as their platform for buying services or products by going through information provided by the companies on their websites.
05 Feb 21
Aromatherapy has become a very popular means of healing and relaxation, and is practiced all over the world today.
05 Feb 21
Recent News
Certified Translation Service
When out there looking for translation services from one dialect to another, you may not know where to start especially if you are a novice in the field.
Christian Translation Service
Translation is not an easy or an obvious procedure. There is a lot that you have to do to achieve your goals as a human translator and as a customer. It also involves vital human technologies that might be quite demanding and taxing to deal with.
Common Franchising Mistakes
While there are some who have succeeded in reaping positive results from their franchise business venture, there are others who have become failures at it. Basically, the dissatisfaction comes from the fact that they have failed to anticipate and understand the dynamics of franchising.
Document Translation, List Of Translation Agencies
Language Consultancy Services Pvt. Ltd. (LCS) is ISO 9001:2008 certified for quality management systems.
French Translation Service
With the high demand for translation services, the numbers of companies offer translation services have also surged and it takes great consideration to find the best firm. At all times, if you are looking for French translation service, you should take your time and find the best provider.
Popular Blogs
05 Feb 21
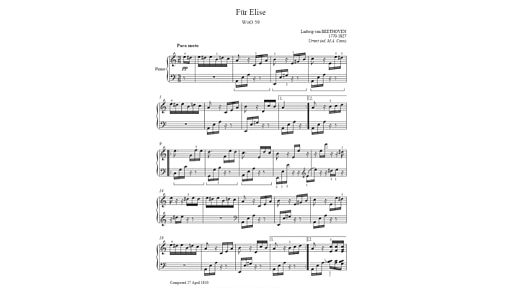
It's a rare parent who wouldn't love their child to take piano lessons. We've all heard of child geniuses like Mozart who began playing and composing at a very tender age, and who wouldn't want their little one to have that same opportunity?While you may be thinking about investing in a piano and lessons for your children, it's also a big expense.
05 Feb 21
Language is always a barrier for businesses to overcome if they are going global. Globalization is one business strategy that is so essential in order to survive in the market. One very effective way to market a business worldwide is to leverage on the power of Internet. That is why you can see more companies are developing websites to establish their global presence.
05 Feb 21
People who suffer from occasional back pain can obtain a great deal of relief by choosing a mattress that provides the support they need to enjoy a good night's rest. Unfortunately, there are a number of myths about what type of mattresses will take pressure off the back, and make it possible to relieve the tension that builds up in the back muscles while sleeping.
Newest Blogs
05 Feb 21
There a few basic tips that you can practice if you want to be sure that you get the best possible fit for the shoes you are looking to purchase. Exactly which steps will be the most important to you will depend on where you are buying the footwear. The internet is quickly becoming the most common place to look for shoes along with retail stores and mail order catalogues.
05 Feb 21
You can see them all around the field, swinging their bats, reaching at made up targets and taking all sorts of actions to enhance their power. The strength behind the swing of the some batters is amazing. The real story, however, it is not only strength that matters. Most of the long ball hitters rely far more on the bat model.
05 Feb 21
All right, I lied. I really can't give you a simple answer to the meaning of life, but if you're looking for a simple explanation of how a lumen is used to measure lights, and why LED lamps are the most efficient way of producing high light output, you've come to the right place. Describing the measurement of light is, by nature, a complex thing.
About Our Company
Our mission has always been a core value of our identity. Learn more about who we are and why we do what we do.
JOIN Our Community
Find friends and other enthusiasts that share your interests. Join our community today and learn and share with others.
Need Help?
Do you have any questions about our website? Send us a quick message and a representative will contact you shortly.